MISC谁偷吃了我的外卖
题目内容:
小凯最近入职了大厂,但是在工作途中出现了一些麻烦事,怎么办呢
首先foremost出来一个压缩包:外卖箱.zip
首先猜测需要提取用户名
1234567891011import zipfiledata= []filename = zipfile.ZipFile('外卖箱.zip').namelist()for i in filename: try: data.append(i[11:-6]) except: passrespice = data[5:]with open('information.txt','w') as file: file.writelines(str(respice))
1234567891011121314151617181920import zipfileimport astwith open('information.txt','r') as r: a = ...
Step1先使用nmap扫描端口
12┌──(root㉿kali)-[~] └─# nmap -p- -sC -sV -T4 10.10.2.72
123456789101112131415161718192021222324252627282930313233343536373839404142434445Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-21 22:00 EST Nmap scan report for 10.10.2.72 Host is up (0.23s latency). Not shown: 65529 closed tcp ports (reset) ...
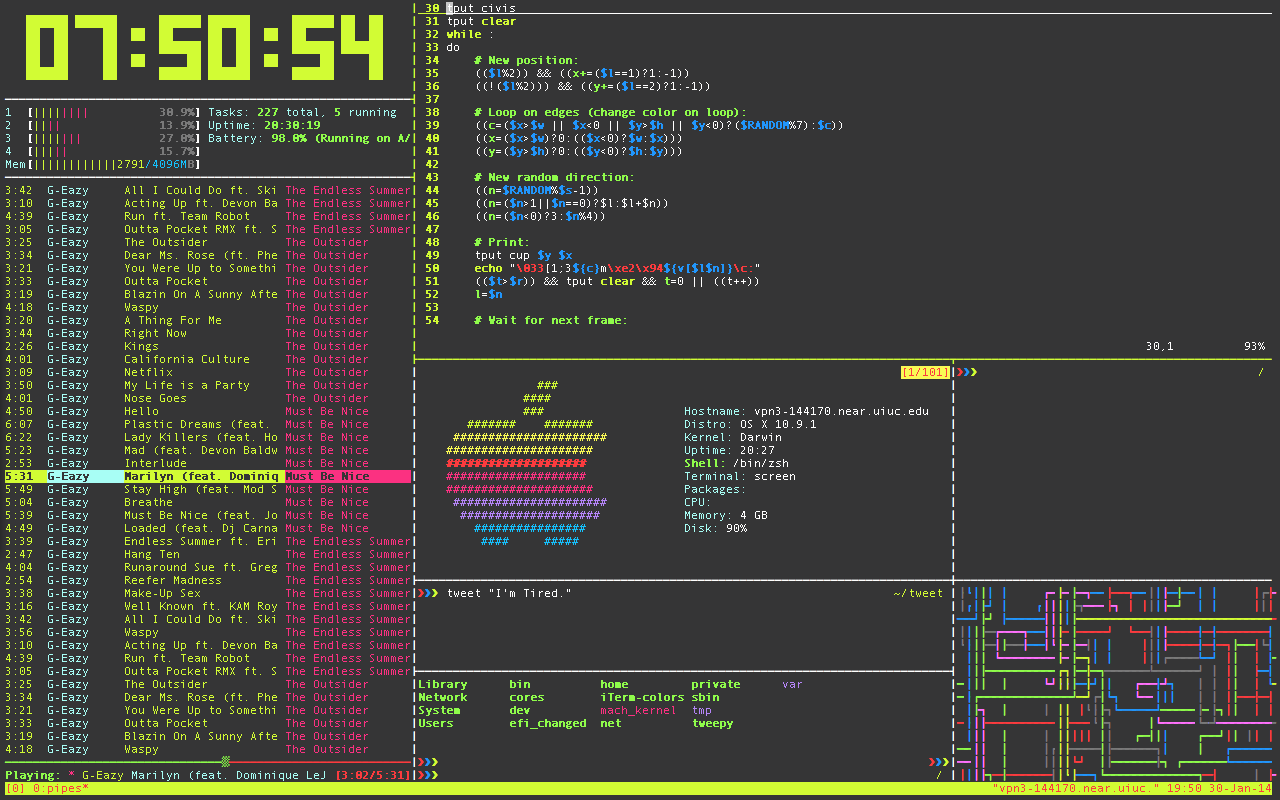
Task 2 Starting tmux “Sessions” and default tmux “prefix”要启动新的 tmux 会话,只需运行不带参数的 tmux 命令即可。第一个会话创建的名称为“0”。默认情况下,tmux 状态栏将为绿色。会话名称位于左侧。窗口在中间,窗口名称在中间。主机名、时间和日期位于底部绿色栏的右侧。
Tmux 不允许在 tmux 中创建嵌套的 tmux,除非您强制这样做。再次运行 tmux 命令时。
我们可以尝试将当前的tmux会话名称从“0”更改为“box-dev”。在此之前,我们可以首先了解tmux是如何被调用的,tmux会话中的所有命令都以tmux前缀开头,而默认情况下,tmux的前缀组合键为“Ctrl b”。
在tmux组合键前缀之后,我们可以再添加按键“shift $”来改变当前tmux会话的名称,所以完整的键盘输入为:ctrl b shift $
如果需要在当前会话中创建另一个 tmux 会话。将 -d 参数与 tmux 命令一起使用。在不附加到它的情况下生成新的 tmux 会话。在下面的示例图像中。-s 参数用于指定新会话的会话名 ...
Task 1 Screens wishes it was this cool.tmux, the terminal multiplexer,很容易成为 Linux 社区(而不仅仅是渗透测试人员)最常用的工具之一。虽然不是恶意工具,但 tmux 使在整个渗透测试中同时运行任务变得非常容易。在这个入门室中,我们将介绍安装和使用 tmux 中使用的一些最常用的组合键的过程。(注意,这里的安装过程是针对 Kali/Ubuntu 的。
Answer the questions below
首先,让我们继续安装 tmux。这可以在 Ubuntu/Kali 上使用以下命令完成:
1apt-get install tmux
安装 tmux 后,让我们启动一个新会话。我们使用什么命令来启动没有自定义名称的新会话?
1tmux
所有 tmux 命令都以键盘按钮组合开头。这个组合中的第一个键是什么?
1control
How about the second key?请注意,必须同时按下这些键,并在按下组合中的下一个目标键之前松开。
1b
让我们继续从我们新创建的 tmux 会 ...
这个房间将介绍SQLi(手动和通过SQLMap利用这个漏洞),破解用户哈希密码,使用SSH隧道来揭示隐藏的服务,以及使用metasploit有效负载来获得root权限。
Task 1 Deploy the vulnerable machine论坛上拿着狙击手的大型卡通头像叫什么名字?
agent 47
Task 2 Obtain access via SQLi在此任务中,您将了解有关 SQL(结构化查询语言)的更多信息,以及如何潜在地操作查询以与数据库进行通信。
SQL 是一种用于在数据库中存储、编辑和检索数据的标准语言。查询可以如下所示:
1SELECT * FROM users WHERE username = :username AND password := password
在我们的GameZone机器中,当您尝试登录时,它将从您的用户名和密码中获取您输入的值,然后将它们直接插入到上面的查询中。如果查询找到数据,则允许你登录,否则将显示错误消息。
这是一个潜在的漏洞位置,因为您可以输入用户名作为另一个 SQL 查询。这将进行查询写入、放置和执行。
如果我们的用户名是 ad ...
使用 Hydra 暴力破解网站登录,识别并使用公共漏洞,然后提升您在这台 Windows 机器上的权限!
1nmap -p- -sC -sV -T4 10.10.173.96
1234567891011121314151617181920212223242526Nmap scan report for 10.10.173.96Host is up (0.18s latency).Not shown: 65533 filtered tcp ports (no-response)PORT STATE SERVICE VERSION80/tcp open http Microsoft IIS httpd 8.5|_http-server-header: Microsoft-IIS/8.5| http-methods: |_ Potentially risky methods: TRACE|_http-title: hackpark | hackpark amusements| http-robots.txt: 6 disal ...
Initial Access1nmap -p- -sC -sV -T4 10.10.206.74
12345678910111213141516171819202122232425262728Nmap scan report for 10.10.206.74Host is up (0.19s latency).Not shown: 65532 filtered tcp ports (no-response)PORT STATE SERVICE VERSION80/tcp open http Microsoft IIS httpd 7.5|_http-title: Site doesn't have a title (text/html).| http-methods: |_ Potentially risky methods: TRACE|_http-server-header: Microsoft-IIS/7.53389/tcp open ssl/ms-wbt-server?| ssl-cert: Sub ...
网络流量分析网络流量分析是指利用分析技术和统计手段对网络数据包进行处理,从而实现对网络的行为分析、性能分析和故障诊断等。它也是网络取证中经常使用的手段。
在几乎所有的CTF 比赛中,都会涉及对网络流量分析能力的考查,尤其是在企业或者行业内部的比赛中,此类题目属于必考题目。这类题目的难度适中,涉及的知识面广泛,能有效结合企业内部的业务,因此建议各位读者重点关注并熟练掌握。
进行网络流量分析需要掌握多方面的知识,不仅涉及杂项知识,还需要结合 Web 渗透等方面的基础知识。
网络协议的基础知识网络协议是为在网络中进行数据交换而建立的规则、标准或约定的集合,通常也简称为协议。互联网的核心是一系列协议,总称为互联网协议(Internet Protocol Suite),它们对计算机如何连接和组网做出了详尽的规定,一个协议通常只为一个目的而设计。那么应该如何设计网络协议呢?
ARPANET(阿帕网)是美国国防高级研究计划局开发的世界上第一个运营的数据包交换网络,是全球互联网的鼻祖。但是,ARPANET 无法和使用不同操作系统的计算机进行网络交流,这引发了研究者的思考。ARPANET的研制经验表明, ...
Hack into a Mr. Robot themed Windows machine. Use metasploit for initial access, utilise powershell for Windows privilege escalation enumeration and learn a new technique to get Administrator access.
Initial Access1nmap -p- -sC -sV -T4 10.10.153.112
123456789101112131415161718192021222324252627282930313233343536373839404142434445464748495051525354PORT STATE SERVICE VERSION80/tcp open http Microsoft IIS httpd 8.5|_http-server-header: Microsoft-IIS/8.5|_http-tit ...
123456789101112131415161718192021222324252627282930313233343536373839404142434445464748495051525354555657585960616263646566676869707172┌──(root㉿kali)-[~]└─# nmap -p- -sC -sV -T4 10.10.189.80 Starting Nmap 7.94SVN ( https://nmap.org ) at 2024-01-07 03:51 ESTNmap scan report for 10.10.189.80Host is up (0.23s latency).Not shown: 65524 closed tcp ports (reset)PORT STATE SERVICE VERSION21/tcp open ftp ProFTPD 1.3.522/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.7 (Ubunt ...